Lets Encrypt 를 사용한 Kubeflow TLS on Istio
Setting Cert-Manager
ClusterIssuer
---
apiVersion: cert-manager.io/v1
kind: ClusterIssuer
metadata:
name: letsencrypt-staging
spec:
acme:
server: https://acme-staging-v02.api.letsencrypt.org/directory
email: altair@megazone.com
privateKeySecretRef:
name: letsencrypt-staging
solvers:
- http01:
ingress:
class: istio
---
apiVersion: cert-manager.io/v1
kind: ClusterIssuer
metadata:
name: letsencrypt-prod
spec:
acme:
server: https://acme-v02.api.letsencrypt.org/directory
email: altair@megazone.com
privateKeySecretRef:
name: letsencrypt-prod
solvers:
- http01:
ingress:
class: istio
YAML
복사
Certificate
---
apiVersion: cert-manager.io/v1
kind: Certificate
metadata:
name: letsencrypt-cert-staging
namespace: istio-system # Ingressgateway와 같은 namespace
spec:
secretName: letsencrypt-cert-staging-tls
dnsNames:
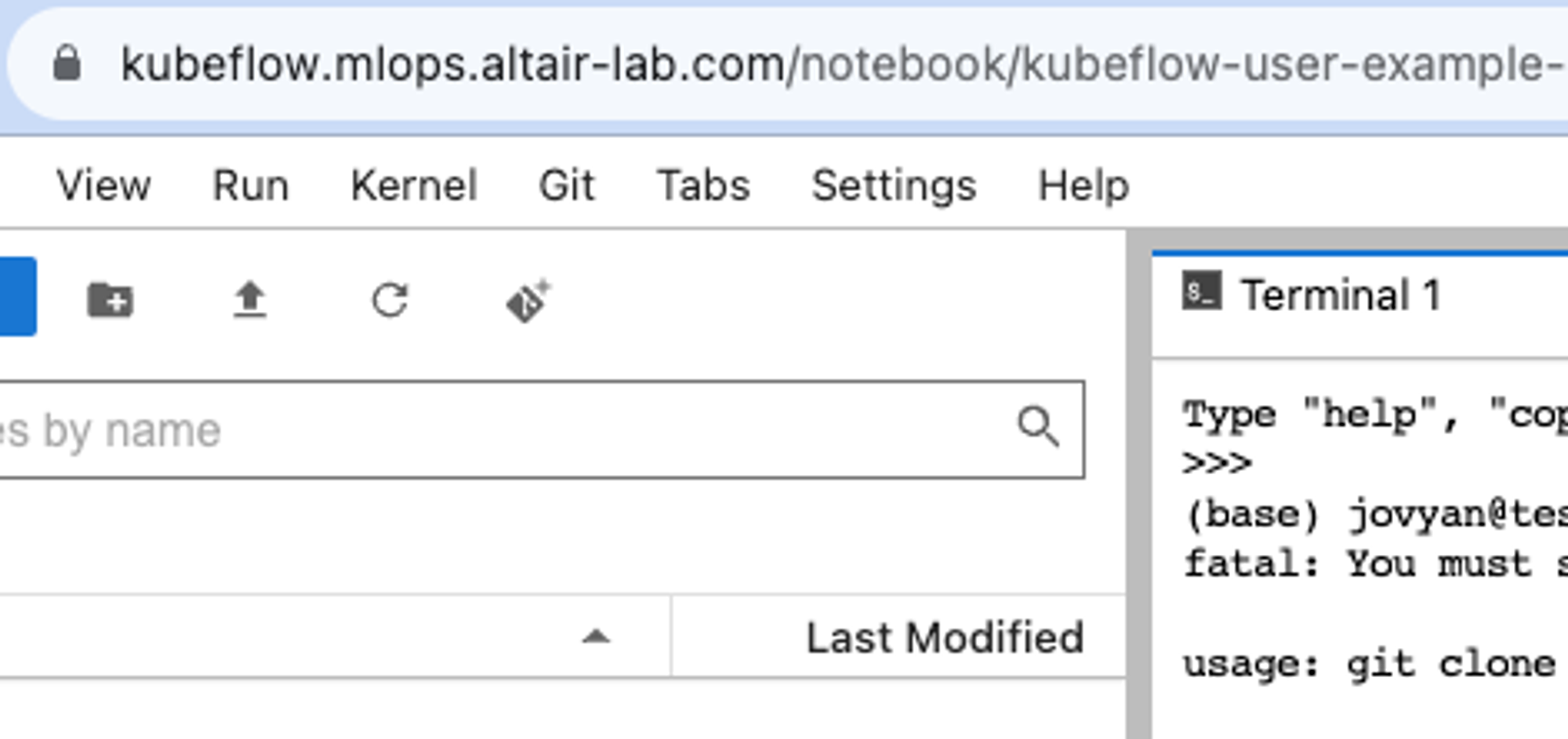
- "kubeflow.mlops.altair-lab.com"
issuerRef:
name: letsencrypt-staging
kind: ClusterIssuer
---
apiVersion: cert-manager.io/v1
kind: Certificate
metadata:
name: letsencrypt-cert-prod
namespace: istio-system
spec:
secretName: letsencrypt-cert-prod-tls
dnsNames:
- "kubeflow.mlops.altair-lab.com"
# WildCard 안먹음
issuerRef:
name: letsencrypt-prod
kind: ClusterIssuer
YAML
복사
Setting Istio
kubeflow gateway
apiVersion: networking.istio.io/v1beta1
kind: Gateway
metadata:
annotations:
kubectl.kubernetes.io/last-applied-configuration: |
{"apiVersion":"networking.istio.io/v1alpha3","kind":"Gateway","metadata":{"annotations":{},"name":"kubeflow-gateway","namespace":"kubeflow"},"spec":{"selector":{"istio":"ingressgateway"},"servers":[{"hosts":["*"],"port":{"name":"http","number":80,"protocol":"HTTP"}}]}}
creationTimestamp: "2023-08-08T05:00:49Z"
generation: 6
name: kubeflow-gateway
namespace: kubeflow
resourceVersion: "856546"
uid: 26a95cb4-5b75-4be6-9014-38105d26df3c
spec:
selector:
istio: ingressgateway
servers:
- hosts:
- '*'
port:
name: http
number: 80
protocol: HTTP
tls:
httpsRedirect: true
- hosts:
- '*'
port:
name: https
number: 443
protocol: HTTPS
tls:
credentialName: letsencrypt-cert-prod-tls # Certificate의 secretName
mode: SIMPLE
YAML
복사
Setting OIDC Params
kubeflow manifest OIDC
vi {kubeflow PATH}/manifests/common/oidc-authservice/base/params.env
OIDC_PROVIDER=http://dex.auth.svc.cluster.local:5556/dex
OIDC_AUTH_URL=/dex/auth
OIDC_SCOPES=profile email groups
AUTHSERVICE_URL_PREFIX=/authservice/
SKIP_AUTH_URLS=/dex,/.well-known
# /.well-known 경로로 하기 때문 Let`s Encrypt Check
AFTER_LOGOUT_URL=/
USERID_HEADER=kubeflow-userid
USERID_PREFIX=
USERID_CLAIM=email
PORT="8080"
STORE_PATH=/var/lib/authservice/data.db
Bash
복사
적용
# Params 변경 적용
cd {kubeflow PATH}/manifests
kustomize build common/oidc-authservice/base | kubectl apply -f -
# OIDC Redirect Rollout Restart
kubectl rollout restart statefulset -n istio-system authservice
Bash
복사